Access Management Policy Template
Access Management Policy Template - Web you can use this sample policy as a starting point to build a pam policy for your organization. For more information about using aws cloudformation. Web you can use the aws management console, aws cli, or aws api to create customer managed policies in iam. Web the policy templates are provided courtesy of the state of new york and the state of california. Web this tool contains four sample policies that define procedures for ensuring that access to all systems and applications is properly approved and monitored. Discover, manage, protect & audit privileged access for your company at lightning speed Web free customizable privileged access management policy template. Web use the workload view in clickup to monitor and review user access on an ongoing basis, ensuring compliance with your access policies. These are free to use and fully customizable to your company's it security practices. Discover, manage, protect & audit privileged access for your company at lightning speed Discover, manage, protect & audit privileged access for your company at lightning speed Discover, manage, protect & audit privileged access for your company at lightning speed Web this tool contains four sample policies that define procedures for ensuring that access to all systems and applications is properly approved and monitored. For more information about using aws cloudformation. Web access management. Web access control protects against unauthorized access to a computer system by using identification, authorization, authentication, and access approval techniques. Web access management is the process of identifying, tracking, controlling, and managing user access rights to information systems. Web fully customizable privileged access management policy template increase understanding and oversight of privileged access management with a pam policy. Web use. Web you can use the aws management console, aws cli, or aws api to create customer managed policies in iam. Web access management is the process of identifying, tracking, controlling, and managing user access rights to information systems. Any user who requests access to. A document designed for compliance with iso 27001:2022, iso 27001:2013, soc2 and pcidss. Web fully customizable. The templates can be customized and used as an outline of an organizational. Ad with delinea™, experience seamless and personalized privileged access management. 24 oct, 2019, 08:01 et. Any user who requests access to. Web access control protects against unauthorized access to a computer system by using identification, authorization, authentication, and access approval techniques. These templates should be used during the onboarding. Web fully customizable privileged access management policy template increase understanding and oversight of privileged access management with a pam policy. Web access management authentication authorization federation bring your own identity credential, access management policy reason for the policy appropriate security. Web access control protects against unauthorized access to a computer system by. Web sans has developed a set of information security policy templates. Web access control protects against unauthorized access to a computer system by using identification, authorization, authentication, and access approval techniques. Discover, manage, protect & audit privileged access for your company at lightning speed These are free to use and fully customizable to your company's it security practices. Web access. Edit the document's elements with our online. Web sans has developed a set of information security policy templates. Web all systems and applications must use encrypted authentication mechanisms and abide by the following: One of the first steps to privileged access management success is defining clear and. Web access management authentication authorization federation bring your own identity credential, access management. Train and educate users on access. Ad with delinea™, experience seamless and personalized privileged access management. Easily find the policy management systems you're looking for w/ our comparison grid. Discover, manage, protect & audit privileged access for your company at lightning speed Edit the document's elements with our online. These are free to use and fully customizable to your company's it security practices. Protecting access to it systems and applications is critical to maintain the integrity of the northwestern polytechnic (“nwp”, or “the institution”). Web you can use this sample policy as a starting point to build a pam policy for your organization. Discover, manage, protect & audit privileged. Web this tool contains four sample policies that define procedures for ensuring that access to all systems and applications is properly approved and monitored. Access control policies, models, and mechanisms. Ad no matter your mission, get the right policy management systems to accomplish it. One of the first steps to privileged access management success is defining clear and. Web access. Web access management authentication authorization federation bring your own identity credential, access management policy reason for the policy appropriate security. For more information about using aws cloudformation. Web the policy templates are provided courtesy of the state of new york and the state of california. Web free customizable privileged access management policy template. Discover, manage, protect & audit privileged access for your company at lightning speed Train and educate users on access. 24 oct, 2019, 08:01 et. Discover, manage, protect & audit privileged access for your company at lightning speed Web sans has developed a set of information security policy templates. One of the first steps to privileged access management success is defining clear and. Ad no matter your mission, get the right policy management systems to accomplish it. Ad with delinea™, experience seamless and personalized privileged access management. Edit the document's elements with our online. Web usage guidelines for each of the access templates is outlined on the team member enablement's handbook page. These are free to use and fully customizable to your company's it security practices. • authentication credentials will not be coded into programs or queries. Web you can use the aws management console, aws cli, or aws api to create customer managed policies in iam. Protecting access to it systems and applications is critical to maintain the integrity of the northwestern polytechnic (“nwp”, or “the institution”). Easily find the policy management systems you're looking for w/ our comparison grid. Web you can use this sample policy as a starting point to build a pam policy for your organization. Web the policy templates are provided courtesy of the state of new york and the state of california. A document designed for compliance with iso 27001:2022, iso 27001:2013, soc2 and pcidss. Web you can use the aws management console, aws cli, or aws api to create customer managed policies in iam. Web access management authentication authorization federation bring your own identity credential, access management policy reason for the policy appropriate security. Web use the workload view in clickup to monitor and review user access on an ongoing basis, ensuring compliance with your access policies. These templates should be used during the onboarding. Web access management is the process of identifying, tracking, controlling, and managing user access rights to information systems. Web this tool contains four sample policies that define procedures for ensuring that access to all systems and applications is properly approved and monitored. Web organizations planning to implement an access control system should consider three abstractions: One of the first steps to privileged access management success is defining clear and. Web fully customizable privileged access management policy template increase understanding and oversight of privileged access management with a pam policy. Web sans has developed a set of information security policy templates. • authentication credentials will not be coded into programs or queries. Ad with delinea™, experience seamless and personalized privileged access management. Ad no matter your mission, get the right policy management systems to accomplish it. Web you can use this sample policy as a starting point to build a pam policy for your organization.Nist Access Control Policy Template
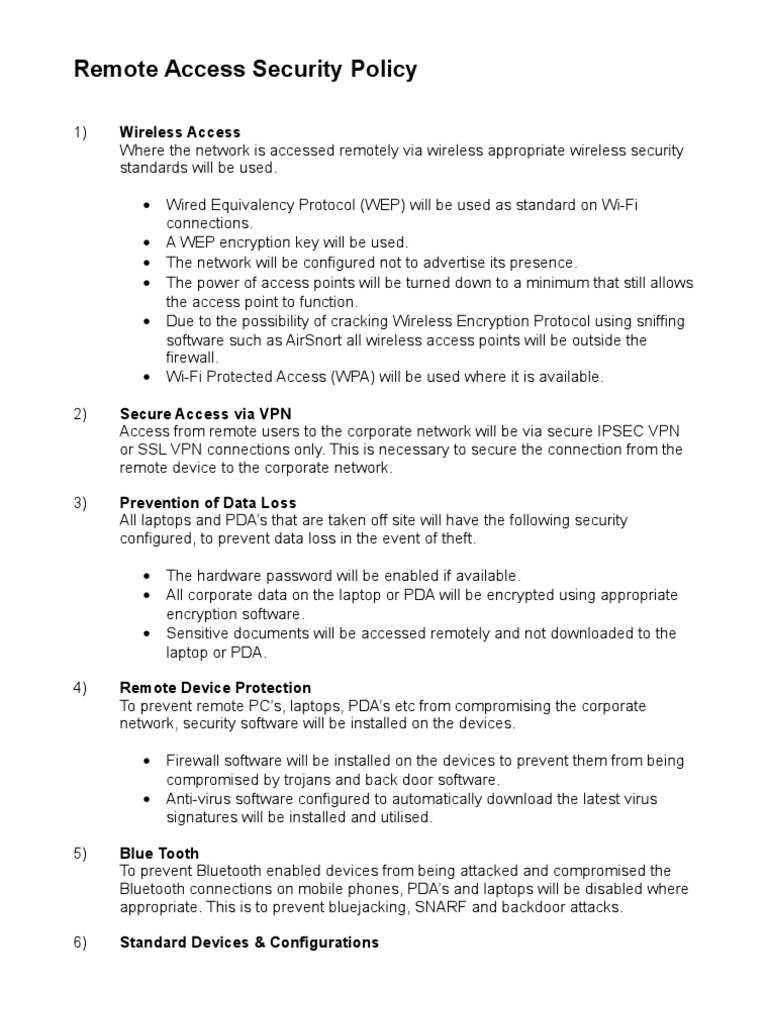
Remote Access Policy Word Template PDF Wi Fi Wireless Access Point
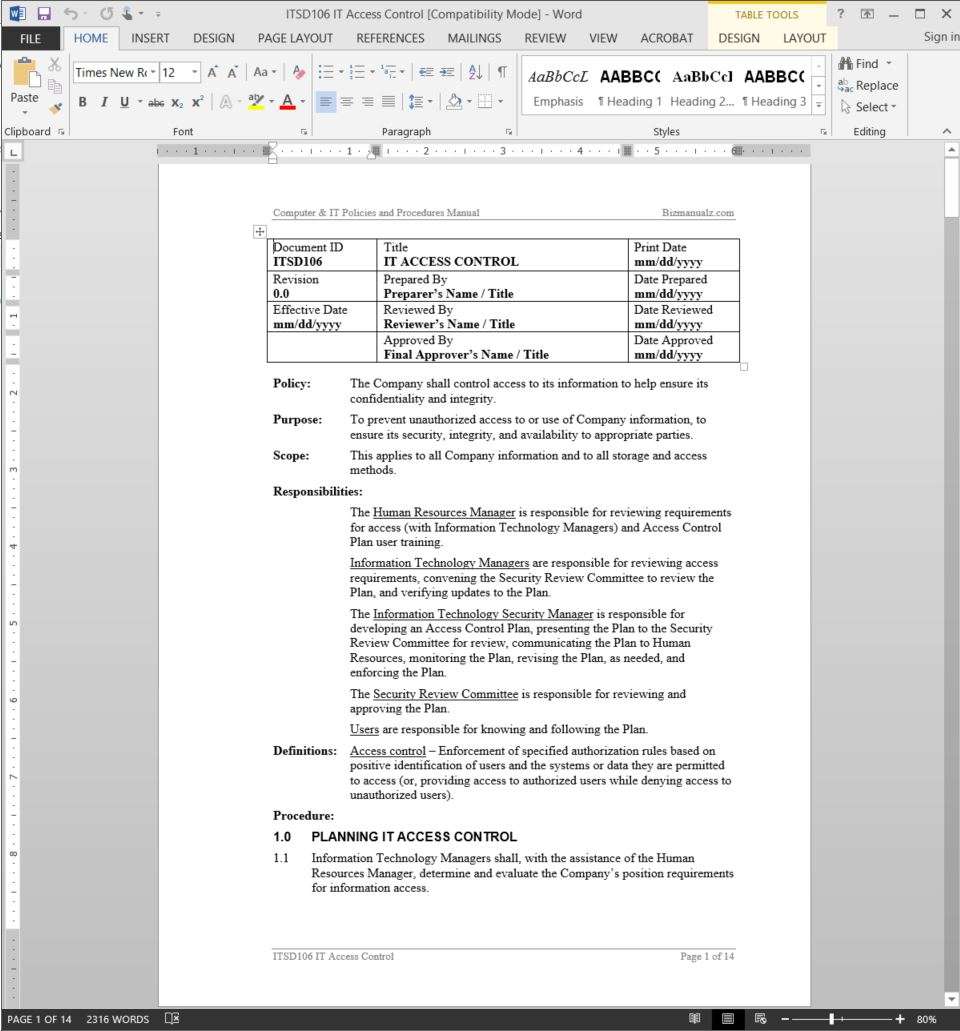
IT Access Control Policy Access Control Policies And Procedures
Standard Access Control Policy Template Free Download
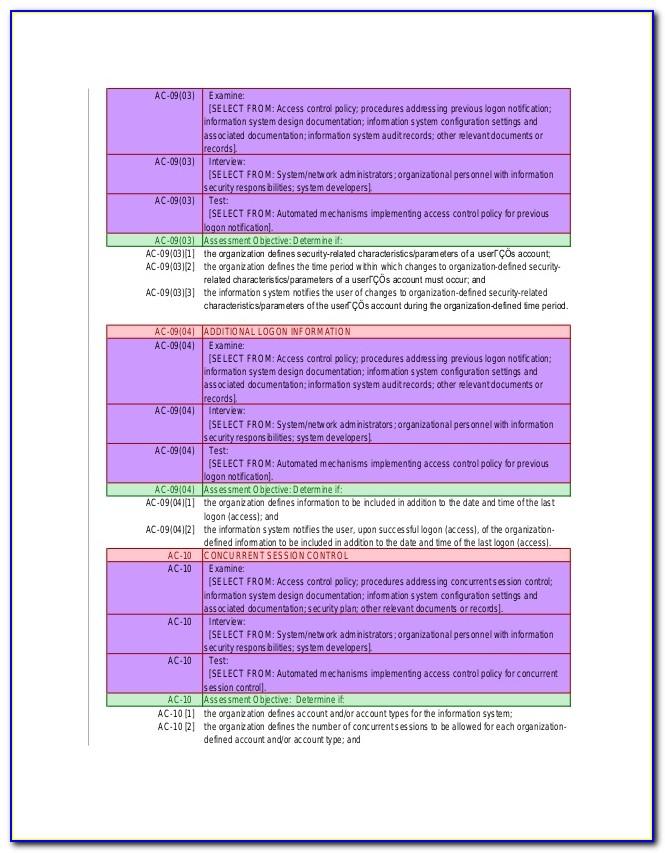
1.07 Secure Data Center Access Policy Exports Government Information
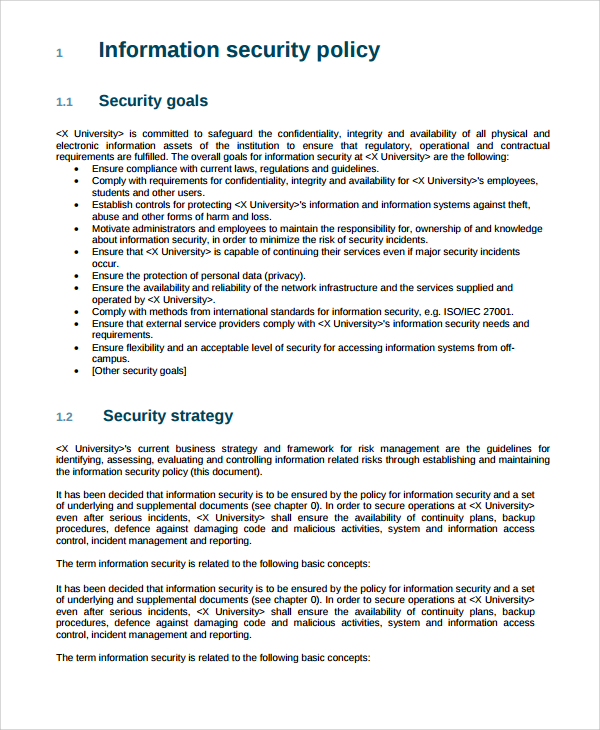
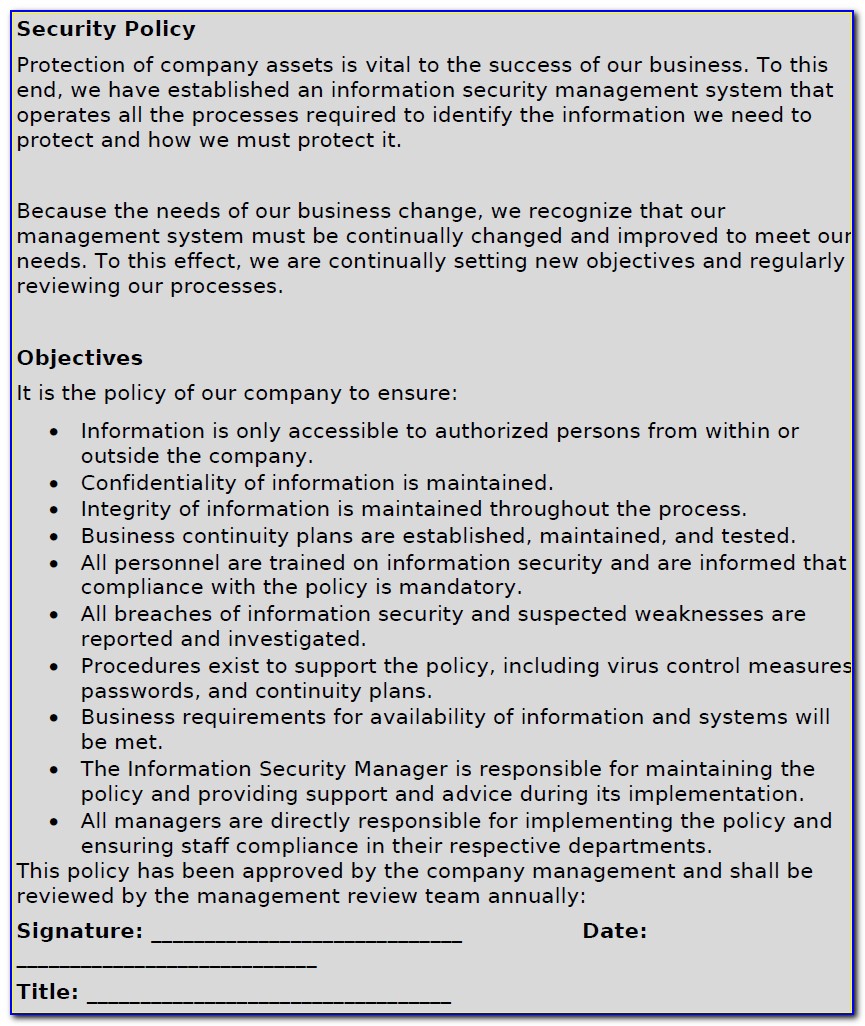
Sample IT Security Policy Template 9+ Free Documents Download in Word
Iso 27001 Isms Policy Template
Standard Access Control Policy Template Free Download
Standard Access Control Policy Template Free Download
Standard Access Control Policy Template Free Download
Web Access Control Protects Against Unauthorized Access To A Computer System By Using Identification, Authorization, Authentication, And Access Approval Techniques.
Train And Educate Users On Access.
These Are Free To Use And Fully Customizable To Your Company's It Security Practices.
For More Information About Using Aws Cloudformation.
Related Post: