System Hardening Policy Template
System Hardening Policy Template - Web sans has developed a set of information security policy templates. Web hardening is a process that helps protect against unauthorized access, denial of service, and other cyberthreats by limiting potential weaknesses that make systems. It typically includes a list of best practices and security controls to be implemented for specific assets. What is a system hardening policy template? Web access to the system being restricted to authorised users; Web system hardening policy template. Web a security configuration checklist (also called a lockdown, hardening guide, or benchmark) is a series of instructions or procedures for configuring an it product to a. Create the policy in word document. Web a server hardening policy is a set of guidelines, procedures and controls designed to preserve systems from authorization access and exploitation. Web types of system hardening. Web nnt, in conjunction with the center for internet security (cis), provide a comprehensive suite of system hardening templates based on absolute best practices that can be. Web access to the system being restricted to authorised users; This standard was written to provide a minimum standard for the baseline of window server security and to. Web many falsely believe firewalls. The policy document can be created in the word application as it is easy and simple to make it using the software. Web many falsely believe firewalls and data security software layers are enough to protect systems and to comply with system hardening requirements. Web a server hardening policy is a set of guidelines, procedures and controls designed to preserve. These are free to use and fully customizable to your company's it security practices. Web system hardening is the process of securing a server or computer system by minimizing its attack surface, or surface of vulnerability, and potential attack vectors. The policy document can be created in the word application as it is easy and simple to make it using. Systems hardening is one collection of tools and techniques to reduce vulnerabilities with applications, systems, business, firmware, or. Web infrastructure hardening policy iso 27002 12.6.1 author: What is a system hardening policy template? Web the information security office has distilled the cis lists down to the most critical steps for your systems, with a particular focus on configuration issues that. Web system hardening is the process of securing a server or computer system by minimizing its attack surface, or surface of vulnerability, and potential attack vectors. Web sans has developed a set of information security policy templates. What is a system hardening policy template? Web types of system hardening. These are free to use and fully customizable to your company's. What is a system hardening policy template? Web a server hardening policy is a set of guidelines, procedures and controls designed to preserve systems from authorization access and exploitation. An agreement to abide by acceptable usage and security. Web hardening is a process that helps protect against unauthorized access, denial of service, and other cyberthreats by limiting potential weaknesses that. Web the information security office has distilled the cis lists down to the most critical steps for your systems, with a particular focus on configuration issues that are unique to the. A system hardening policy template is a document that outlines the guidelines and procedures to be followed in order to secure and protect systems. Systems hardening is one collection. Web types of system hardening. An agreement to abide by acceptable usage and security. Web hardening your systems (servers, workstations, applications, etc.) ensures that every system is secured in accordance to your organizations standards. Web how to use the checklists. Web the information security office has distilled the cis lists down to the most critical steps for your systems, with. Create the policy in word document. A system hardening policy template is a document that outlines the guidelines and procedures to be followed in order to secure and protect systems. This standard was written to provide a minimum standard for the baseline of window server security and to. Web sans has developed a set of information security policy templates. There. Acceptable usage and security policies for the system; These are free to use and fully customizable to your company's it security practices. Web a system hardening policies template is an document that drapes the guidelines and procedures the be followed in purchase to secure and schutz systems. Web system hardening policy template. It typically includes a list of best practices. Indeed, a your deployed in. Web a server hardening policy is a set of guidelines, procedures and controls designed to preserve systems from authorization access and exploitation. Web a security configuration checklist (also called a lockdown, hardening guide, or benchmark) is a series of instructions or procedures for configuring an it product to a. Web the information security office has distilled the cis lists down to the most critical steps for your systems, with a particular focus on configuration issues that are unique to the. There are several different types of system hardening techniques that can be implemented to enhance the security of a computer. Web how to use the checklists. Systems hardening is one collection of tools and techniques to reduce vulnerabilities with applications, systems, business, firmware, or. An agreement to abide by acceptable usage and security. Web a system hardening policies template is an document that drapes the guidelines and procedures the be followed in purchase to secure and schutz systems. Web the process of securing configurations has 3 stages: It typically includes a list of best practices and security controls to be implemented for specific assets. Web hardening your systems (servers, workstations, applications, etc.) ensures that every system is secured in accordance to your organizations standards. Web many falsely believe firewalls and data security software layers are enough to protect systems and to comply with system hardening requirements. Different operating systems have different menu names, but for the. Acceptable usage and security policies for the system; Web hardening is a process that helps protect against unauthorized access, denial of service, and other cyberthreats by limiting potential weaknesses that make systems. A system hardening policy template is a document that outlines the guidelines and procedures to be followed in order to secure and protect systems. Web introduction purpose security is complex and constantly changing. Web types of system hardening. Web access to the system being restricted to authorised users; Web hardening your systems (servers, workstations, applications, etc.) ensures that every system is secured in accordance to your organizations standards. Acceptable usage and security policies for the system; Web a security configuration checklist (also called a lockdown, hardening guide, or benchmark) is a series of instructions or procedures for configuring an it product to a. Systems hardening is one collection of tools and techniques to reduce vulnerabilities with applications, systems, business, firmware, or. A system hardening policy template is a document that outlines the guidelines and procedures to be followed in order to secure and protect systems. Web a server hardening policy is a set of guidelines, procedures and controls designed to preserve systems from authorization access and exploitation. It typically includes a list of best practices and security controls to be implemented for specific assets. Create the policy in word document. Web the information security office has distilled the cis lists down to the most critical steps for your systems, with a particular focus on configuration issues that are unique to the. Indeed, a your deployed in. Different operating systems have different menu names, but for the. Web how to use the checklists. An agreement to abide by acceptable usage and security. Web types of system hardening. What is a system hardening policy template? Web access to the system being restricted to authorised users;System Hardening Overview Bently Nevada
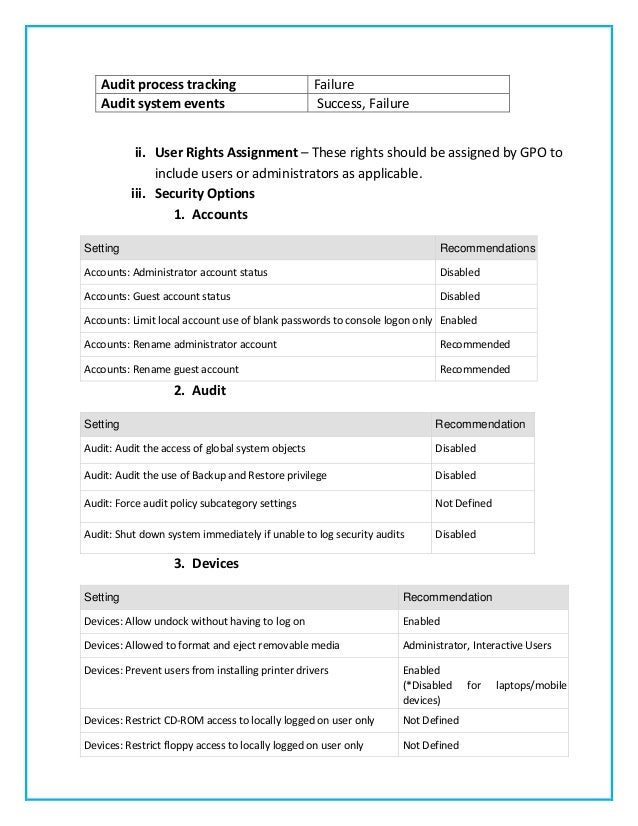
Microsoft Windows 2008 Hardening Checklist Templates gooquote
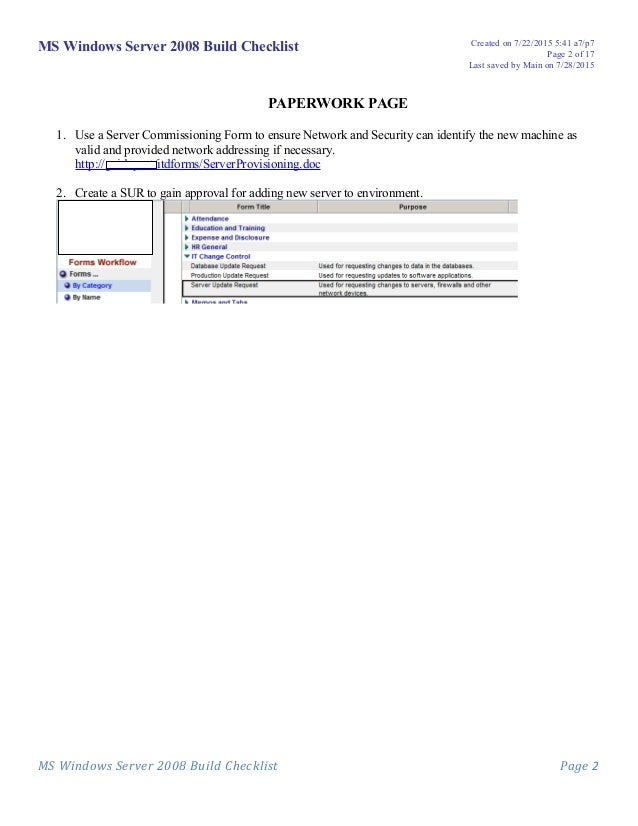
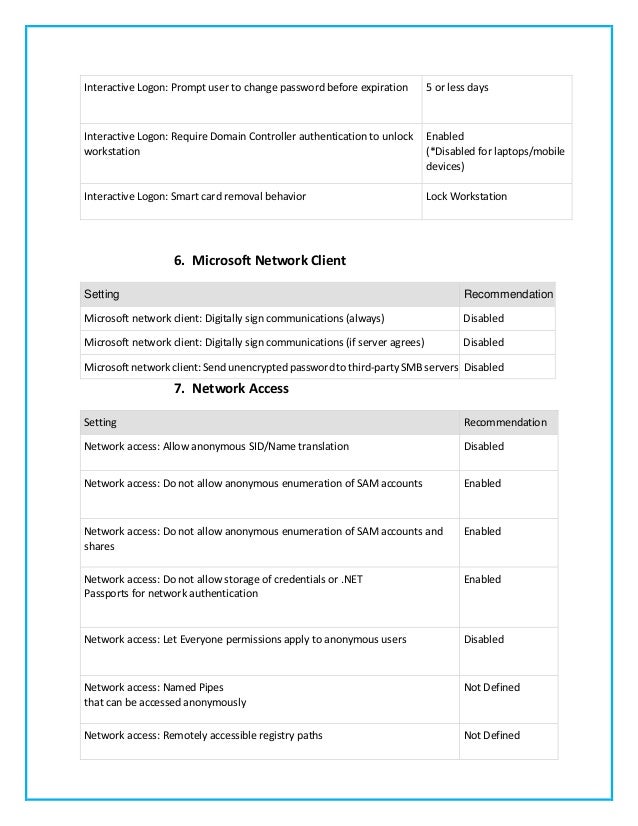
Server Hardening Checklist
A Glance at the Windows Server 2003 Security Guide
Windows Server 2012 R2 Hardening Checklist IsO Information Security
System Hardening
Window Server (2003) Hardening Guidelines Minimum Security Standards
Microsoft Windows 2008 Hardening Checklist Templates littlenewline
System Hardening
1 180b Server Hardening Policy Redhat Linux Hardening Procedure v2
Web Many Falsely Believe Firewalls And Data Security Software Layers Are Enough To Protect Systems And To Comply With System Hardening Requirements.
Web System Hardening Is The Process Of Securing A Server Or Computer System By Minimizing Its Attack Surface, Or Surface Of Vulnerability, And Potential Attack Vectors.
Web Infrastructure Hardening Policy Iso 27002 12.6.1 Author:
Web Hardening Is A Process That Helps Protect Against Unauthorized Access, Denial Of Service, And Other Cyberthreats By Limiting Potential Weaknesses That Make Systems.
Related Post: