Vulnerability Management Program Template
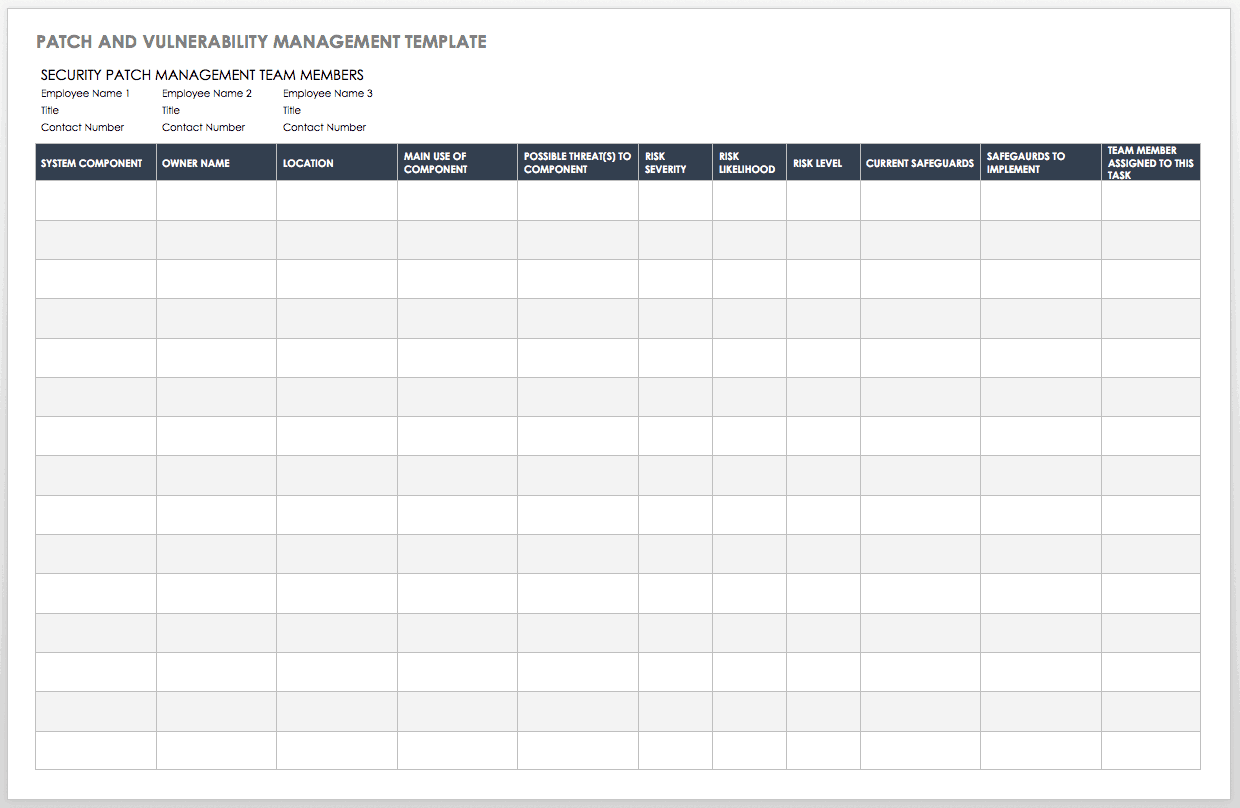
Vulnerability Management Program Template - Getapp has helped more than 1.8 million businesses find the best software for their needs. Web may 16, 2022 9 mins threat and vulnerability management security experts share their best advice for the essential ingredients of a solid vulnerability. Web vulnerability management recommendations focus on addressing issues related to continuously acquiring, assessing, and acting on new information in order to. Web the sans vulnerability management maturity model helps you gauge the effectiveness of your vulnerability management program. Ad stay compliant across regulations and build customer trust with onetrust. Web download our free vulnerability management policy template now. 5 metrics to start measuring in your vulnerability management program, we covered 5 metrics to. Web we have provided everything you need to create a vulnerability management policy for your organization. The cwe refers to vulnerabilities while the cve pertains. Web this vulnerability management plan template is designed for it leaders and teams who are looking to create a plan to manage and mitigate vulnerabilities in their systems. Compare and analyze aging data by the severity of vulnerabilities and their share: Web during the webcast vulnerability management metrics part 1: Web download our free vulnerability management policy template now. Web this guide is intended for organizations seeking help in establishing a vulnerability management process. Download template purpose the purpose of the (company) vulnerability management policy. 5 metrics to start measuring in your vulnerability management program, we covered 5 metrics to. Web abstract this document provides guidance on creating a security patch and vulnerability management program and testing the effectiveness of that program. Ad respond to cyber attacks & recover critical data. Web the ncsr question set represents the national institute of standards and technology cybersecurity. Web download our free vulnerability management policy template now. Web we have provided everything you need to create a vulnerability management policy for your organization. Web abstract this document provides guidance on creating a security patch and vulnerability management program and testing the effectiveness of that program. 5 metrics to start measuring in your vulnerability management program, we covered 5. Read how to succeed with irm and maintain resilience as work flows across the enterprise. Powered by vmware carbon black. Reduce your cost of compliance up to 60% and obtain certifications 50% faster. Web may 16, 2022 9 mins threat and vulnerability management security experts share their best advice for the essential ingredients of a solid vulnerability. Vulnerability management is. Reduce your cost of compliance up to 60% and obtain certifications 50% faster. This guide gives the correlation between 49 of. Web this guide is intended for organizations seeking help in establishing a vulnerability management process. Mgt516 helps you think strategically about vulnerability management in order. Ad learn why integrated risk management is a necessary ingredient in digital transformation. Ad respond to cyber attacks & recover critical data. Ad stay compliant across regulations and build customer trust with onetrust. 5 metrics to start measuring in your vulnerability management program, we covered 5 metrics to. Web may 16, 2022 9 mins threat and vulnerability management security experts share their best advice for the essential ingredients of a solid vulnerability. Mgt516. Powered by vmware carbon black. Web vulnerability management recommendations focus on addressing issues related to continuously acquiring, assessing, and acting on new information in order to. Download template purpose the purpose of the (company) vulnerability management policy. Reduce your cost of compliance up to 60% and obtain certifications 50% faster. Mgt516 helps you think strategically about vulnerability management in order. Web we have provided everything you need to create a vulnerability management policy for your organization. The cwe refers to vulnerabilities while the cve pertains. Web may 16, 2022 9 mins threat and vulnerability management security experts share their best advice for the essential ingredients of a solid vulnerability. Download template purpose the purpose of the (company) vulnerability management policy.. Download template purpose the purpose of the (company) vulnerability management policy. Vulnerability management is a continuous, proactive, and often automated process that keeps your computer systems, networks, and. Powered by vmware carbon black. Web mgt516 is based on the prepare, identify, analyze, communicate, and treat (piact) model. Ad protect your data, applications, and infrastructure in one managed security solution. Web mgt516 is based on the prepare, identify, analyze, communicate, and treat (piact) model. Web this guide is intended for organizations seeking help in establishing a vulnerability management process. Ad stay compliant across regulations and build customer trust with onetrust. Web the ncsr question set represents the national institute of standards and technology cybersecurity framework (nist csf). Ad protect your. Compare and analyze aging data by the severity of vulnerabilities and their share: Web this vulnerability management plan template is designed for it leaders and teams who are looking to create a plan to manage and mitigate vulnerabilities in their systems. The cwe refers to vulnerabilities while the cve pertains. Web this guide is intended for organizations seeking help in establishing a vulnerability management process. Ad stay compliant across regulations and build customer trust with onetrust. Web the sans vulnerability management maturity model helps you gauge the effectiveness of your vulnerability management program. Read how to succeed with irm and maintain resilience as work flows across the enterprise. Web download your template today! Web during the webcast vulnerability management metrics part 1: Web vulnerability management recommendations focus on addressing issues related to continuously acquiring, assessing, and acting on new information in order to. Web may 16, 2022 9 mins threat and vulnerability management security experts share their best advice for the essential ingredients of a solid vulnerability. Ad stay compliant across regulations and build customer trust with onetrust. Mgt516 helps you think strategically about vulnerability management in order. Reduce your cost of compliance up to 60% and obtain certifications 50% faster. Getapp has helped more than 1.8 million businesses find the best software for their needs. This guide gives the correlation between 49 of. Ad respond to cyber attacks & recover critical data. Ad learn why integrated risk management is a necessary ingredient in digital transformation. Ad protect your data, applications, and infrastructure in one managed security solution. Web we have provided everything you need to create a vulnerability management policy for your organization. Compare and analyze aging data by the severity of vulnerabilities and their share: Web this guide is intended for organizations seeking help in establishing a vulnerability management process. The cwe refers to vulnerabilities while the cve pertains. Web we have provided everything you need to create a vulnerability management policy for your organization. Ad learn why integrated risk management is a necessary ingredient in digital transformation. Mgt516 helps you think strategically about vulnerability management in order. Creating and implementing an vulnerability management policies and procedures is a vital component of any company’s cyber. Reduce your cost of compliance up to 60% and obtain certifications 50% faster. Web abstract this document provides guidance on creating a security patch and vulnerability management program and testing the effectiveness of that program. Powered by vmware carbon black. Ad stay compliant across regulations and build customer trust with onetrust. Vulnerability management is a continuous, proactive, and often automated process that keeps your computer systems, networks, and. Web the sans vulnerability management maturity model helps you gauge the effectiveness of your vulnerability management program. This guide gives the correlation between 49 of. Web mgt516 is based on the prepare, identify, analyze, communicate, and treat (piact) model. Web the ncsr question set represents the national institute of standards and technology cybersecurity framework (nist csf).Top Vulnerability Management Program Template Life Cycle Management
Vulnerability Management Program Template in 2021 Program template
Free Vulnerability Assessment Templates Smartsheet
Free Vulnerability Assessment Plan Template Google Docs, Word, Apple
Vulnerability Management Program Template Stcharleschill Template
Free Vulnerability Assessment Plan Template Google Docs, Word, Apple
Free Vulnerability Assessment Templates Smartsheet (2023)
Fantastic Vulnerability Management Program Template Report template
Fresh Vulnerability Management Program Template Sparklingstemware
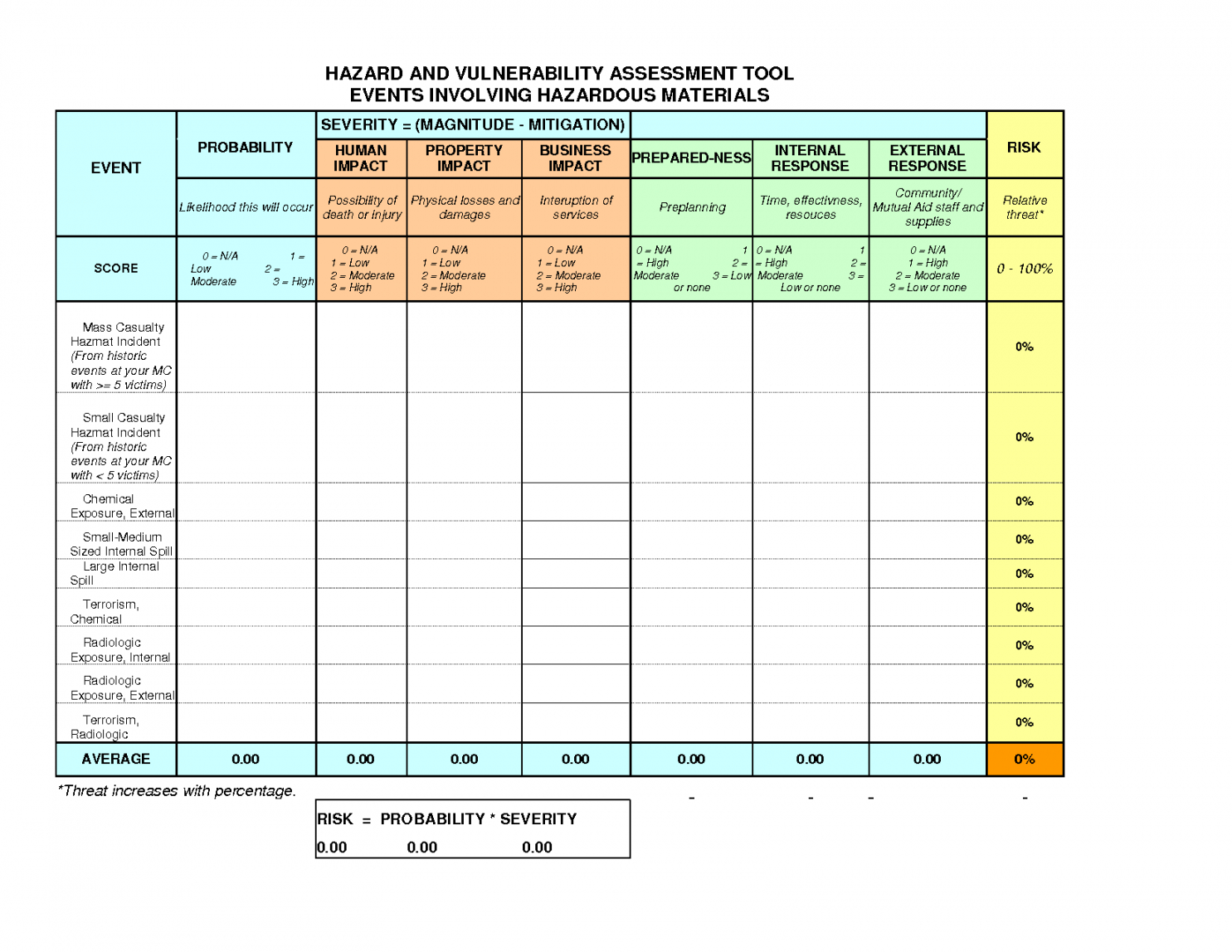
Editable Updated Guidelines For Fast Systems In Hazard Assessment
Web The Sans Vulnerability Management Maturity Model Helps You Gauge The Effectiveness Of Your Vulnerability Management Program.
Ad Stay Compliant Across Regulations And Build Customer Trust With Onetrust.
Web This Vulnerability Management Plan Template Is Designed For It Leaders And Teams Who Are Looking To Create A Plan To Manage And Mitigate Vulnerabilities In Their Systems.
The Process Areas Described Include • Developing A.
Related Post: